Firewalls in Modern Network Security: Types, Layers, and Deployment Strategies
Firewalls are a fundamental component of modern network security, acting as a barrier between trusted and untrusted environments. They monitor and control incoming and outgoing network traffic based on predefined security rules. As cyber threats have become more sophisticated, firewalls have evolved from simple filtering devices into complex, intelligent security systems capable of deep inspection and threat detection.
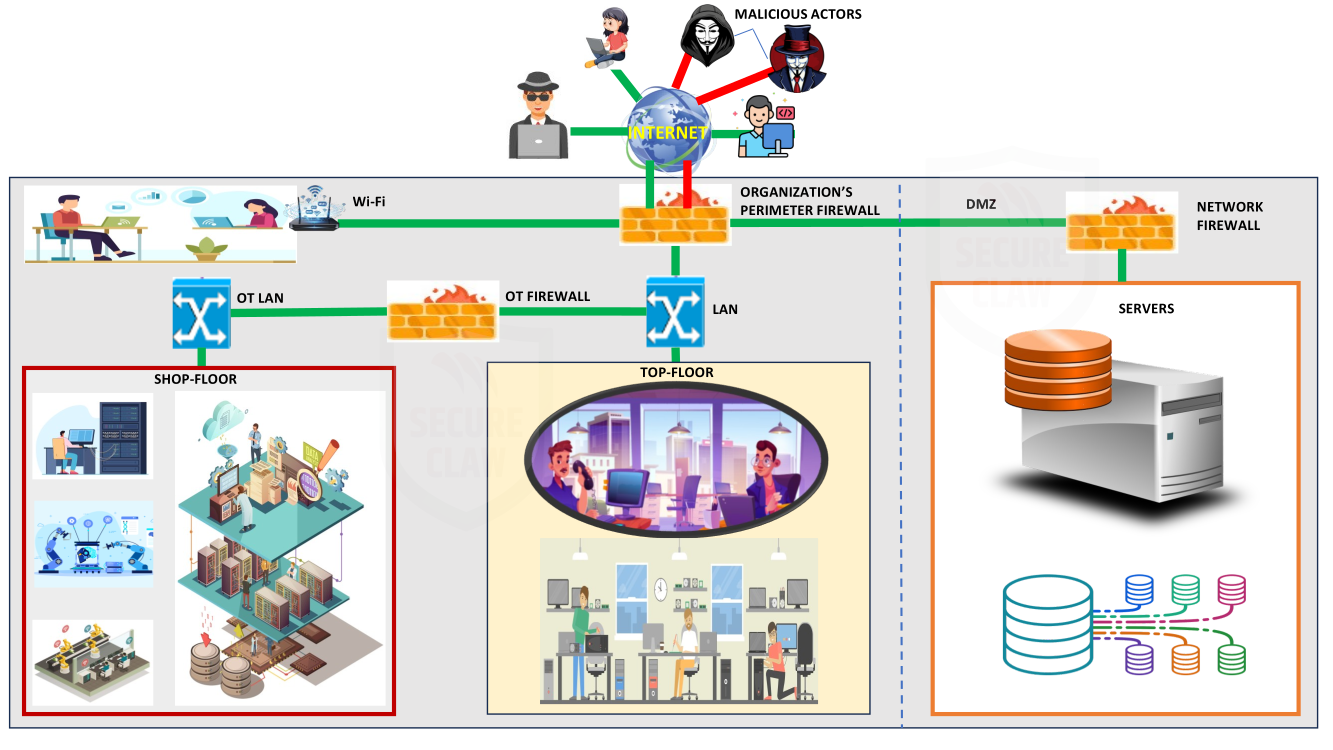
In today's interconnected world, organizations rely heavily on firewalls not only to protect sensitive data but also to ensure continuous and secure operations. Firewalls are deployed at multiple levels of a network architecture, from internet gateways to internal segments and industrial control systems. Their proper use reduces vulnerabilities and enhances overall cybersecurity posture.
"The effectiveness of a network's security is not determined by the presence of a firewall, but by the wisdom applied in selecting, designing, and positioning it within the architecture. A well-chosen, well-configured, and well-audited firewall becomes not just a barrier, but a strategic safeguard for the entire organization."
Dr. Shekhar A Pawar CEO, SecureClaw
Forms of Firewalls: Software and Hardware
Software Firewalls
Software firewalls are installed directly on host devices such as personal computers, servers, or virtual machines. They provide system-level protection by controlling which applications can send or receive data over the network.
These firewalls are particularly effective in protecting endpoints against unauthorized access and malware activity. They can be configured to block suspicious applications, restrict ports, and monitor user-level activity. However, since each device requires its own firewall installation and management, maintaining consistency across large networks can be challenging. Additionally, heavy firewall processing may consume system resources, impacting device performance.
Hardware Firewalls
Hardware firewalls are standalone devices placed between networks to filter traffic at a centralized point. They are commonly deployed at network perimeters, such as between an organization's internal network and the internet.
These firewalls offer robust protection by handling high volumes of traffic efficiently. They can enforce consistent policies across entire networks, making them suitable for enterprises. Moreover, they are less vulnerable to attacks targeting individual systems since they operate independently. However, they require initial investment, proper setup, and ongoing maintenance to ensure optimal performance.
Firewall Capabilities in Layer 3 Devices
Modern networking devices have evolved to integrate multiple functionalities. Many Layer 3 devices, such as routers and multilayer switches, now include built-in firewall features.
This integration allows organizations to simplify their network infrastructure by combining routing and security functions into a single device. These devices can enforce access rules, filter traffic, and protect against basic threats. At the same time, modern firewalls include routing capabilities, allowing them to determine traffic paths while enforcing security policies. This convergence improves efficiency but requires administrators to carefully configure devices to avoid security gaps, routing issues, or performance bottlenecks.
Firewall Types Based on OSI Layers
Packet Filtering Firewall (Layer 3)
Packet filtering firewalls inspect packets based on header information such as IP addresses, port numbers, and protocols. They make decisions quickly, allowing or blocking traffic based on predefined rules.
While they are efficient and introduce minimal delay, they lack the ability to analyze the actual data contained within packets. This limitation makes them less effective against modern attacks that exploit application-level vulnerabilities. As a result, they are often used as a basic security layer rather than a complete solution.
Stateful Inspection Firewall (Layer 3/4)
Stateful firewalls enhance security by maintaining a record of active connections. They analyze not only individual packets but also the context of ongoing communications.
This ability allows them to determine whether incoming traffic is part of an established and legitimate session. By doing so, they prevent unauthorized or suspicious traffic from entering the network. Although more secure than packet filtering, they require more processing power and careful configuration.
Circuit-Level Gateway (Layer 5)
Circuit-level gateways focus on monitoring session establishment, particularly during the TCP handshake process. They verify that connections are legitimate before allowing communication to proceed.
These firewalls help conceal internal network structure, adding a layer of anonymity. However, since they do not inspect data content, they cannot detect application-based threats, making them less effective for comprehensive security.
Application Layer Firewall (Layer 7)
Application-layer firewalls provide deep packet inspection by analyzing the content of traffic. They understand application protocols such as HTTP, FTP, and SMTP.
This enables them to detect and block malicious content, including malware, unauthorized commands, and suspicious data patterns. Although they offer strong protection, they can introduce latency due to the complexity of analysis and require more system resources.
Next-Generation Firewall (NGFW)
Next-generation firewalls combine multiple security technologies into one platform. They include features like intrusion detection and prevention, application awareness, user authentication, and deep inspection.
These firewalls provide comprehensive security across multiple layers, making them highly effective against modern cyber threats. Despite their advantages, they require skilled management and regular updates to remain effective.
Additional Specialized Firewall Types
Web Application Firewall (WAF)
WAFs are designed specifically to protect web applications by filtering HTTP and HTTPS traffic. They analyze requests and responses to identify malicious inputs.
They are essential for protecting web-based services from common attacks such as SQL injection and cross-site scripting. As organizations increasingly rely on web applications, WAFs have become a critical component of cybersecurity strategy.
Cloud-Based Firewall (FWaaS)
Cloud firewalls deliver security services through the cloud, enabling organizations to protect users and systems regardless of location.
They are highly scalable and can be centrally managed, making them suitable for modern distributed networks. However, their effectiveness depends on reliable internet connectivity and proper integration with existing systems.
Virtual Firewalls
Virtual firewalls operate within virtualized environments and protect virtual machines and networks.
They are essential in cloud computing and data centers where traditional hardware boundaries do not exist. These firewalls provide flexibility and scalability but require careful configuration to manage virtual network complexity.
Industrial Firewalls
Industrial firewalls are designed for environments such as manufacturing and automation systems. They focus on maintaining stable and continuous operations.
They are optimized for low latency and high reliability, ensuring that industrial processes are not interrupted. These firewalls are critical for safeguarding operational technology systems from cyber threats.
Firewall Deployment Zones
DMZ (Demilitarized Zone)
The DMZ is a separate network segment used to host public-facing services. It acts as a buffer zone between the internal network and external networks.
By isolating these services, organizations reduce the risk of direct attacks on internal systems. Even if a server in the DMZ is compromised, attackers cannot easily access the internal network.
Internal Network Segmentation
Internal segmentation involves dividing a network into smaller sections to improve security.
Firewalls enforce boundaries between departments or systems, preventing threats from spreading. This approach supports modern security strategies such as zero trust, where no user or system is automatically trusted.
Industrial / PLC Zone
Firewalls in industrial zones protect critical systems such as PLCs and automation equipment.
These zones require strict control because they directly impact physical processes. Proper segmentation ensures that cyber threats do not interfere with operational systems.
Operational Technology (OT) Firewalls
OT firewalls are specialized for industrial systems and critical infrastructure. They focus on protecting physical processes rather than just data.
They can interpret industrial protocols like Modbus and DNP3, ensuring secure communication between industrial devices. These firewalls are crucial in environments where system failure could lead to safety risks or financial loss.
Additionally, OT firewalls are engineered for reliability, operating continuously without causing delays. As industrial systems become more connected, these firewalls help bridge security gaps between IT and operational technology environments.
Internal Network Segmentation
Internal segmentation involves dividing a network into smaller sections to improve security.
Firewalls enforce boundaries between departments or systems, preventing threats from spreading. This approach supports modern security strategies such as zero trust, where no user or system is automatically trusted.
Firewall Operating Modes
Routed Mode (Layer 3)
In routed mode, the firewall functions as a network gateway with assigned IP addresses.
It routes traffic between networks while enforcing security policies. This mode allows advanced features such as NAT and traffic segmentation, making it widely used in modern network design.
Transparent Mode (Layer 2)
Transparent mode allows the firewall to operate as a bridge, filtering traffic without changing IP addressing.
This makes it easy to deploy in existing networks without reconfiguration. It is often used when adding security to legacy systems.
Hybrid Mode
Hybrid mode combines both routed and transparent functionalities.
This approach provides flexibility, allowing organizations to design customized security architectures based on their needs.
Cybersecurity Configuration and Audit Importance
Firewall effectiveness depends heavily on correct configuration and ongoing audits.
Proper configuration ensures that only necessary traffic is allowed, following the principle of least privilege. Misconfigurations can lead to serious vulnerabilities or network disruptions.
Regular audits help identify outdated rules, errors, and security gaps. Logging and monitoring further enhance visibility, enabling early detection of threats. Together, these practices ensure that firewalls remain effective and compliant with security standards.
Importance of Firewall Design and Placement
Firewalls must be strategically placed within a network to maximize their effectiveness.
Proper placement ensures that all critical traffic is inspected and controlled. Factors such as traffic flow, network topology, and redundancy must be considered during design.
Poor placement can lead to security gaps or performance issues, while well-designed deployment improves both protection and efficiency.
Emerging Firewall Strategies for Quantum Cybersecurity
As quantum computing advances, it poses a significant threat to traditional encryption methods such as RSA (Rivest-Shamir-Adleman) and elliptic curve cryptography, which are widely used in firewall-secured communications like VPNs and HTTPS. To address this emerging risk, firewall technologies are evolving toward quantum-resilient security models rather than relying solely on conventional filtering techniques. One of the most important developments is the integration of post-quantum cryptography (PQC) into next-generation firewalls, enabling them to use encryption algorithms that are resistant to quantum attacks. Additionally, modern firewalls are being designed to support quantum-safe VPNs, which use hybrid cryptographic approaches to ensure secure communication during the transition period. Alongside cryptographic improvements, architectural changes such as Zero Trust security models are gaining importance, where every connection is continuously verified, reducing dependence on encryption alone.
Furthermore, Artificial intelligence (AI) driven and behavior-based firewalls are emerging to detect anomalies and unknown attack patterns, providing an additional layer of defense even if encryption is compromised. In advanced environments, emerging technologies like Quantum Key Distribution (QKD) are also being explored to enhance secure communication through physics-based key exchange mechanisms. Overall, the future of firewall security in the quantum era lies in a combination of adaptive encryption, intelligent detection, and robust network design rather than a single standalone solution.
"In the era of quantum computing, firewall security must evolve beyond traditional encryption boundaries, embracing quantum-resilient intelligence and adaptive trust mechanisms; only then can it truly safeguard the future of digital and industrial ecosystems."
Dr. Shekhar A Pawar CEO, SecureClaw
As A Conclusion:
Firewalls have evolved into sophisticated, multi-layered security systems essential for modern networks. They protect data, applications, and industrial systems across various environments.
Their effectiveness depends on selecting the right type, deploying them strategically, and maintaining proper configuration. With continuous monitoring and improvement, firewalls remain a critical defense against evolving cyber threats.